Beyond the Firewall: Securing the Software Supply Chain in 2026
For decades, cybersecurity was defined by the “castle and moat” analogy. If you built a strong enough firewall, your data was safe. However, as we move through 2026, the perimeter has completely dissolved. Modern software is no longer a monolithic block of custom code; it is a sprawling web of open-source dependencies, third-party APIs, and AI-generated snippets.
The greatest threat to the tech sector today isn’t a hacker “breaking in” through your front door—it’s a vulnerability “walking in” through your supplier’s back door. Welcome to the era of Software Supply Chain Integrity.
The New Attack Vector: Upstream Compromise
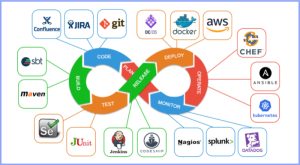
In 2026, attackers have pivoted their focus “upstream.” Instead of targeting a single enterprise, they target the libraries and tools that thousands of enterprises use. By compromising a popular open-source package or a widely used CI/CD tool, a single exploit can cascade through the global tech ecosystem.
The data is clear: supply chain attacks have quadrupled over the last few years. Whether it is a malicious “dependency confusion” attack or a compromised GitHub Action, the goal is the same: to inject malicious code into a trusted environment before it ever reaches production.
The Three Pillars of Modern Supply Chain Security
At TechOTD, we’ve identified three critical strategies that every development team must adopt in 2026 to remain resilient.
1. The SBOM Mandate (Software Bill of Materials)
Think of an SBOM as the “nutrition label” for your software. It is a formal, machine-readable record of every library, module, and dependency used to build an application. In 2026, providing an SBOM is no longer a “nice-to-have”; it is a regulatory requirement for many enterprise contracts.
By maintaining a real-time SBOM, security teams can respond to new vulnerabilities (CVEs) in seconds rather than days. If a critical flaw is found in a minor utility library, an SBOM tells you exactly which of your products are affected and where they are deployed.
2. Guarding AI-Generated Code
The rise of “Vibe Coding” and AI agents has introduced a new type of risk: AI-generated security debt. AI models are designed to be helpful, but they lack context and judgment. They may suggest code that is functional but uses outdated, insecure encryption or references deprecated libraries.
Securing the supply chain in 2026 means implementingAutomated AI Guardrails. Every line of code suggested by an AI must pass through an automated “security lens”—AI-powered SAST (Static Application Security Testing) tools that scan for logic flaws and insecure patterns in real-time within the developer’s IDE.
3. Identity-First Security and Non-Human Identities (NHIs)
The “login” is the new break-in point. As we move toward Agentic AI and automated microservices, the number of “Non-Human Identities”—API keys, service accounts, and tokens—has exploded.
Attackers in 2026 are increasingly targeting these machine identities because they are often over-privileged and rarely rotated. A robust security posture now requiresContinuous Adaptive Authentication, where every request—whether from a human or an AI agent—is verified based on real-time risk signals like geolocation, device health, and behavioral patterns.
From Prevention to “Durable Resilience”
The hard truth of 2026 is that 100% prevention is impossible. The focus has shifted from “How do we stop every attack?” to “How quickly can we recover when a dependency is compromised?”
This is the concept of Durable Resilience. It involves:
-
Chaos Engineering for Security: Purposely “breaking” a dependency in a sandbox to see how the system fails.
-
Crypto-Agility: Building architecture that allows you to swap out compromised encryption algorithms without rebuilding the entire app.
-
Rapid Patching Protocols: Mandating that high-severity vulnerabilities in third-party code must be patched within 24 hours of discovery.
Conclusion: The Developer’s New Mandate
Cybersecurity is no longer a “department”—it is a core feature of high-quality software development. In the tech sector of 2026, the most successful companies will be those that treat their software supply chain with the same scrutiny they apply to their own internal code.