Introduction
We live in an age where data travels faster than thought — from cloud storage to smartphones, from online banking to social media. But as our digital world expands, so do the cyber threats lurking behind every connection.
From global ransomware attacks to phishing scams and data breaches, cybercrime has evolved into one of the biggest challenges of the 21st century. In 2024 alone, the global cost of cybercrime was estimated to surpass $10 trillion, making it more profitable than the illegal drug trade.
In this digital age, cybersecurity isn’t optional — it’s essential for individuals, businesses, and governments alike.
What Is Cybersecurity?
Cybersecurity refers to the practice of protecting systems, networks, and data from unauthorized access, attacks, and damage.
It involves technologies, processes, and best practices designed to secure:
-
Computers and servers
-
Mobile devices
-
Networks
-
Cloud environments
-
User data
Core Objectives of Cybersecurity — The CIA Triad:
| Element | Meaning | Purpose |
|---|---|---|
| Confidentiality | Keeping data private | Prevent unauthorized access |
| Integrity | Maintaining data accuracy | Ensure data isn’t altered maliciously |
| Availability | Ensuring accessibility | Keep systems online and functional |
Together, these principles form the foundation of all cybersecurity systems.
⚙️ Types of Cybersecurity
Cybersecurity covers a wide range of protection layers designed to defend different parts of the digital ecosystem.
1. Network Security
Protects internal networks from intruders using firewalls, intrusion detection systems, and VPNs.
2. Information Security (InfoSec)
Ensures data privacy and protects sensitive information from leaks or misuse.
3. Cloud Security
Secures cloud-based infrastructure, applications, and data stored in remote servers.
4. Endpoint Security
Defends devices such as laptops, phones, and IoT gadgets that connect to a network.
5. Application Security
Prevents vulnerabilities during software development through encryption, code testing, and patch management.
6. Operational Security (OpSec)
Focuses on the policies and procedures to handle data and protect assets.
7. Disaster Recovery and Business Continuity
Ensures systems can recover quickly from attacks or data loss events.
Common Cyber Threats
Cyberattacks come in many forms — some target individuals, others target global corporations.
Here are the most common types of cyber threats:
| Type | Description | Example |
|---|---|---|
| Phishing | Fraudulent emails trick users into revealing credentials | Fake bank alerts |
| Ransomware | Encrypts data and demands payment | WannaCry, LockBit |
| Malware | Software designed to damage or steal information | Viruses, Trojans |
| Denial of Service (DoS/DDoS) | Overloads servers to make them crash | Attacks on websites or networks |
| Man-in-the-Middle (MitM) | Intercepts data during transmission | Wi-Fi eavesdropping |
| SQL Injection | Inserts malicious code into databases | Web form exploits |
| Zero-Day Exploit | Targets unpatched vulnerabilities | Newly discovered software flaws |
| Insider Threats | Employees misuse access privileges | Data theft by insiders |
The increasing sophistication of cyberattacks means no organization is immune — prevention and vigilance are key.
Essential Cybersecurity Tools
Modern cybersecurity strategies rely on a mix of software, AI, and human expertise.
Commonly Used Tools:
-
Antivirus Software: Protects against malware and viruses (e.g., Bitdefender, Norton)
-
Firewalls: Blocks unauthorized access to networks
-
Encryption Tools: Secures data in transit and at rest
-
Password Managers: Protects user credentials
-
VPNs: Masks IP addresses for secure browsing
-
Intrusion Detection Systems (IDS): Monitors networks for suspicious activity
-
Multi-Factor Authentication (MFA): Adds an extra security layer beyond passwords
The Role of Artificial Intelligence in Cybersecurity
AI is becoming a game-changer in the fight against cyber threats.
How AI Helps:
-
Detects anomalies in real-time
-
Predicts potential attacks before they occur
-
Automates incident response
-
Reduces false alerts and improves accuracy
Example: AI-driven tools like Darktrace and CrowdStrike use machine learning to identify unusual network behavior and block cyberattacks instantly.
Cybersecurity in Business
Organizations of all sizes — from startups to multinationals — are prime targets for hackers.
Key Areas of Focus for Businesses:
-
Employee Awareness Training: Human error is the top cause of breaches.
-
Data Encryption: Sensitive data must be encrypted at all stages.
-
Regular Security Audits: Identify vulnerabilities before hackers do.
-
Zero-Trust Architecture: Verify every access attempt, even inside the network.
-
Incident Response Plans: Prepare for attacks with structured recovery strategies.
Example:
In 2023, several global firms adopted Zero Trust Security Models, ensuring users and devices are verified every time they access company data — drastically reducing internal breaches.
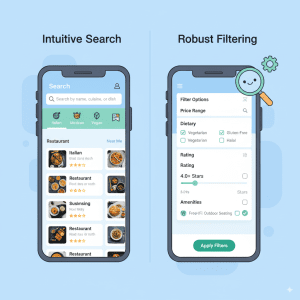
Cybersecurity in the Cloud
With more organizations migrating to cloud services like AWS, Azure, and Google Cloud, securing cloud infrastructure is vital.
Cloud security ensures:
-
Data encryption
-
Identity and access management (IAM)
-
Secure APIs and regular patching
Providers also follow shared responsibility models, meaning both the provider and the client share the duty of maintaining security.
Cybersecurity for Individuals
Cybersecurity isn’t just for corporations — individuals must also stay alert.
Personal Cyber Hygiene Tips:
-
Use strong and unique passwords for every account.
-
Enable two-factor authentication (2FA).
-
Avoid clicking on suspicious links or attachments.
-
Update software and systems regularly.
-
Use secured Wi-Fi networks.
-
Regularly back up important data.
The Future of Cybersecurity
The coming years will see cybersecurity evolve alongside AI, quantum computing, and the Internet of Things (IoT).
🔮 Key Future Trends:
-
AI-powered threat detection
-
Quantum encryption for unbreakable security
-
Zero Trust Architecture becoming the global standard
-
Biometric authentication (face, fingerprint, voice)
-
Cyber resilience — not just prevention but rapid recovery
Cybersecurity is no longer about building walls — it’s about creating adaptive, intelligent systems that learn and evolve faster than attackers.
Conclusion
In the digital era, data is power, and protecting it is non-negotiable.
Cybersecurity is the first line of defense against a world of invisible threats. Whether it’s an individual securing personal data or a multinational corporation safeguarding billions of records, awareness and preparation are the strongest shields.
As technology advances, so must our commitment to cybersecurity — ensuring a safer, more resilient digital future for everyone.
FAQs
1. What is cybersecurity in simple terms?
Cybersecurity is the protection of computers, networks, and data from digital attacks or unauthorized access.
2. Why is cybersecurity important?
It prevents data theft, financial loss, and system damage caused by hackers or malware.
3. What are common cyber threats?
Phishing, ransomware, malware, DDoS attacks, and insider threats are among the most common.
4. How can individuals improve cybersecurity?
Use strong passwords, enable two-factor authentication, and avoid suspicious emails or downloads.
5. What is Zero Trust Security?
It’s a model where every user or device must be verified before gaining access to a network — even those inside the organization.